Page History
...
| Setting | Parameter |
|---|---|
| LDAP Host | 192.168.4.241 |
| LDAP Port | 389 |
| LDAP Base DN | cn=Users,dc=i4,dc=local |
| LDAP Group | CN=Yellowfin Users,CN=Users, CD=i4,CD=local |
| LDAP Bind User | admin@Yellowfin.bi or YELLOWFIN\admin |
| LDAP Bind Password | ********* |
| LDAP Search Attribute | employeeID |
| LDAP First Name Attribute | givenName |
| LDAP Surname Attribute | lastName |
| LDAP Email Attribute | userPrincipleName |
| LDAP Role Attribute | Writer |
| Ordering | LDAP Authentication First |
Description:
- Connect to LDAP host 192.168.4.241 on port 389
- Users will be searched from cn=Users, dc=i4, and dc=local
- Users will be allowed to access Yellowfin if they are a member of cn=Yellowfin Users, cn=Users, dc=i4, or dc=local
- The user search will be conducted with user 'admin', who will get authenticated based on the bind password provided.
- The user will use employeeID as their login ID and Yellowfin will load their given name, surname, and email from the LDAP directory attributes givenName, lastName, and userPrincipleName respectively.
...
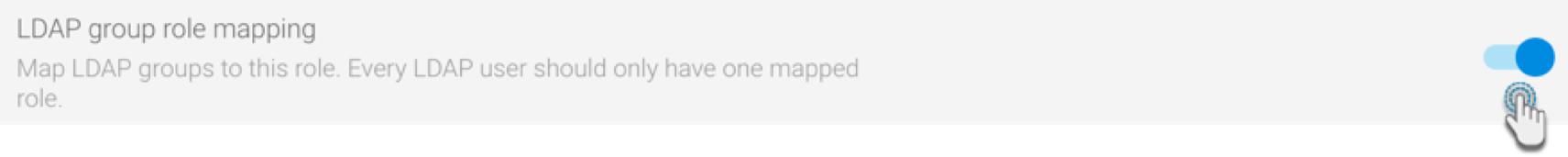
- First, enable this functionality from the LDAP configuration page. Navigate to Administration > Configuration > Authentication page, and expand the LDAP Configuration tab (ensure that LDAP is selected as the chosen method of authentication)
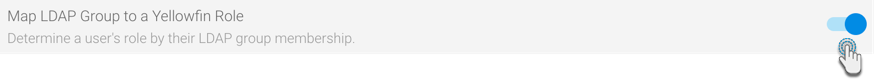
- From this list of configurations, enable the LDAP group role mapping Map LDAP Group to a Yellowfin Role toggle.
- Save the changes.
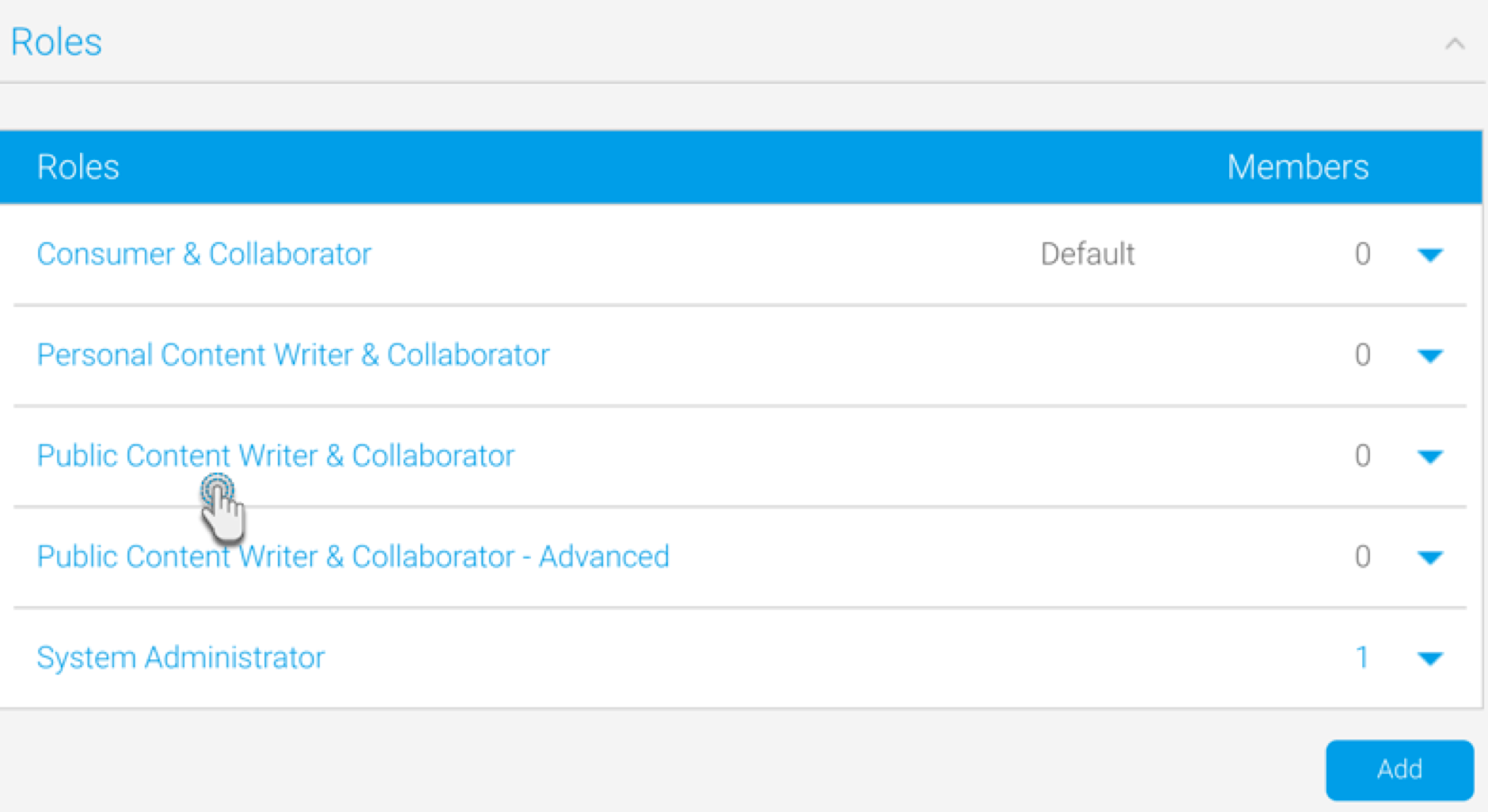
- Navigate to the Admin Console, and from the Roles tab, select a role to associate LDAP groups with.
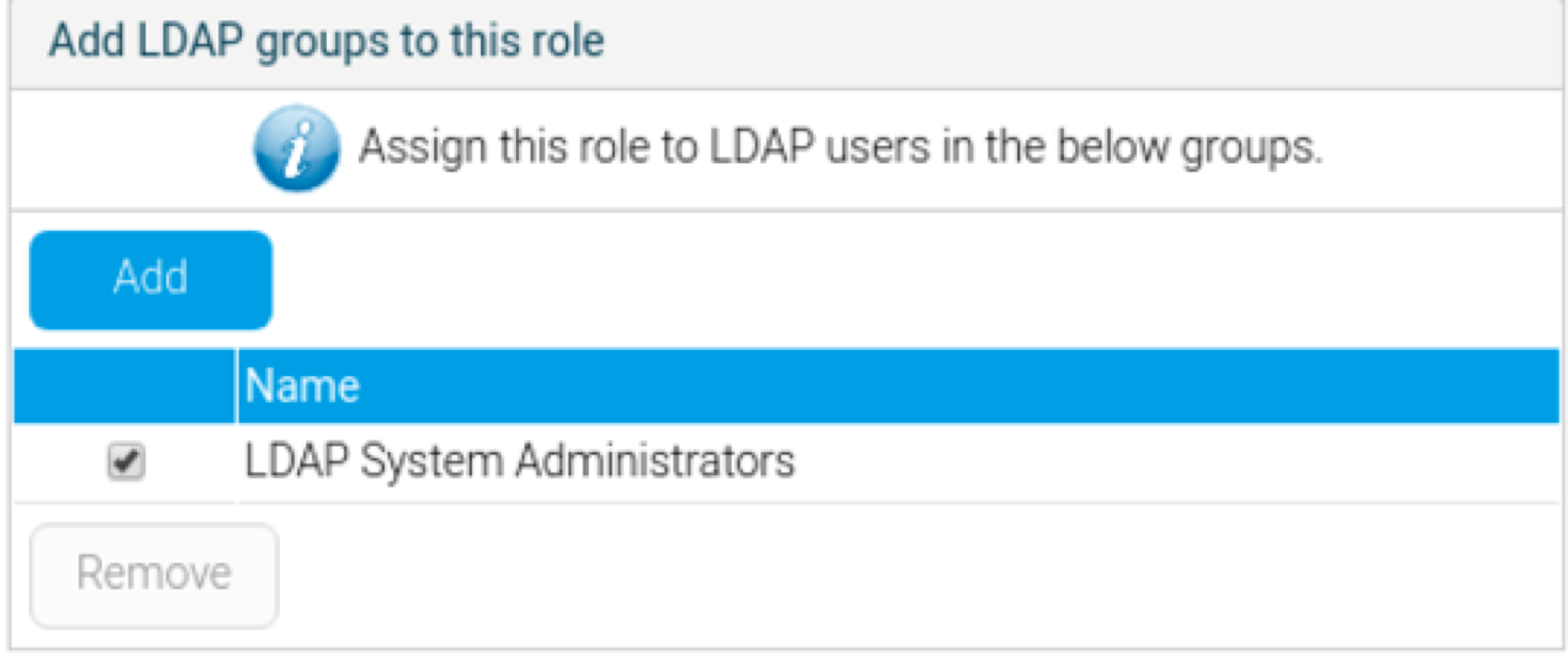
- At the Role page, scroll to the panel titled ‘Add LDAP groups to this role’ (this only appears if the LDAP group role mapping functionality is enabled).
- Add an LDAP group to associate to the selected role.
- Save the settings on the role page.
- Users of this LDAP group will now inherit all the role permissions defined directly here upon logging into Yellowfin.
...