Page History
...
This section provides solutions to the basic problems, such as:
| Anchor | ||||
|---|---|---|---|---|
|
...
onelogin.saml2.idp.x509cert =MIIC2DCCAcCgAwIBAgIQfdRAAWmWko1IsimA004o3TANBgkqhki…
Solution
- Get a valid certificate from AD FS;
- modify onelogin.saml.properties (onelogin.saml2.idp.x509cert);
- restart Yellowfin;
- update Yellowfin SAML Bridge relying party metadata in AD FS.
| Styleclass | ||
|---|---|---|
| ||
...
| Anchor | ||||
|---|---|---|---|---|
|
...
The Original Exception was java.security.InvalidKeyException: Illegal key size
Solution
When inspecting the SAML response payload below, the data is encrypted with AES-256:
Refer to the EncryptionMethod Algorithm here: http://www.w3.org/2001/04/xmlenc#aes256-cbc
By default, Java’s key size is limited to 128-bit key due to US export laws and a few countries’ import laws.
...
- Copy the local_policy.jar and US_export_policy.jar files to this directory: [JAVA_HOME]/jre/lib/security.
...
| Styleclass | ||
|---|---|---|
| ||
...
| Anchor | ||||
|---|---|---|---|---|
|
...
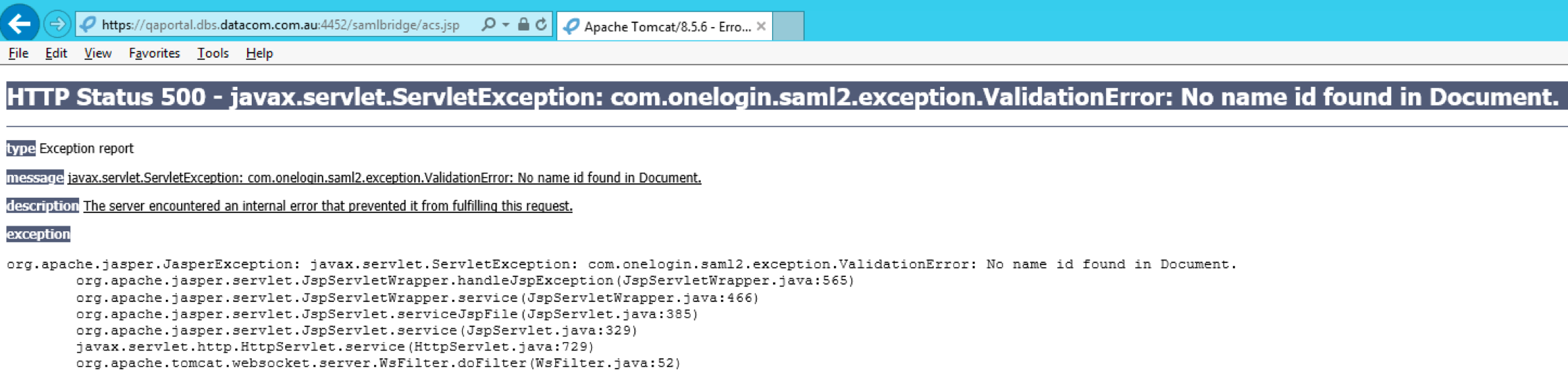
SAML requires the name ID as part of the Identity Provider response. If you provide the incorrect name ID of your AD FS, then you will see the following exception in your browser:
Ensure that you pass the correct name ID and that it matches the format expected by the SAML bridge (that is, onelogin.saml2.sp.nameidformat of onelogin.saml.properties).
...
NAMEID_ENCRYPTED = 'urn:oasis:names:tc:SAML:2.0:nameid-format:encrypted';
...
The example below shows a list of correct Yellowfin logs regarding the SAML response:
...
DEBUG com.onelogin.saml2.SamlAuth - processResponse success --> <very long line representing signing certificate>
...
| Styleclass | ||
|---|---|---|
| ||
...
| Anchor | ||||
|---|---|---|---|---|
|
...
Then it means that you have switched off the user provision functionality, and the passed ID is not of a Yellowfin user.
| Styleclass | ||
|---|---|---|
| ||
...
| Section | |||||||
|---|---|---|---|---|---|---|---|
|
...