Page History
...
Prepare for SAML implementation
| Styleclass | ||
|---|---|---|
| ||
Before setting up SAML within Yellowfin, make sure you have a good understanding of the fields you’ll be required to address. The tables below provide further details for each of the fields.
...
Parameter | Description | Required? | Default |
|---|---|---|---|
Service Provider SSO URL | The SSO Single Sign On endpoint URL that your IdP will use to reach the Yellowfin login page. This is typically your external base URL followed by /SAMLLogin.i4 | Required | ext_base_url/SAMLLogin.i4 |
Audience Restriction | This is sometimes referred to as the ‘Service Provider Entity Id’ or ‘Issuer Id’. It's the identifier of the Yellowfin SAML service. This is typically your external base URL followed by | Required | ext_base_url/SAMLMetadata.i4 |
Encryption Certificate | This certificate is used by the IdP to encrypt traffic going to Yellowfin. As mentioned earlier on this page, you must generate your own SSL key pair and provide the encryption certificate here. | Required if the toggle for Incoming Requests Encrypted is enabled | None |
...
Parameter | Description | Required? | Default | ||
|---|---|---|---|---|---|
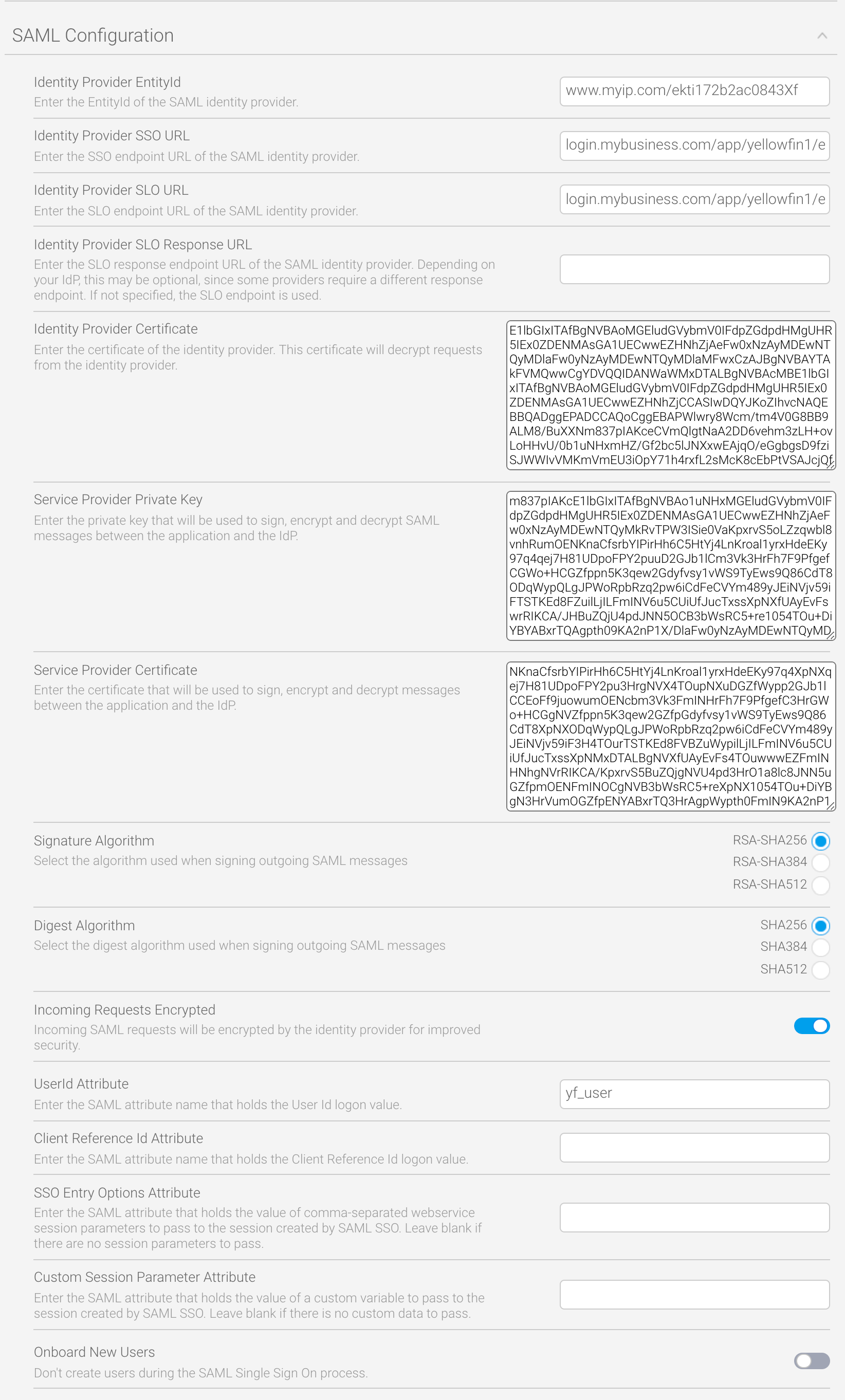
Identity Provider EntityId | Sometimes referred to as the ‘audience URI’ or ‘audience restriction’, this identifies the entity of the service provider. This is typically in the format of <your_idp_domain>/<sp_id> For example, www.okta.com/ekti172b2ac0843Xf | Required | None | ||
Identity Provider SSO URL | The SSO endpoint Single Sign On endpoint URL of the SAML identity provider, which your IdP should display clearly within their own configuration page. This is in the format of: <your_sso_domain>/<path_to_spidp_sso_login> For example, login.mybusiness.com/app/yellowfin1/ekti172b2ac0843Xf/sso | Required | None | ||
Identity Provider Certificate | This certificate decrypts requests from the identity provider. Your identity provider should make this certificate obvious in their configuration. | Required | None | ||
Incoming Certificate Verification Algorithm | This algorithm verifies the incoming identity provider certificate. Choose from three different hash lengths to match whatever your incoming certificate uses:
| Required | SHA256 | ||
Incoming Requests Encrypted | This toggle dictates whether incoming SAML requests will be encrypted by the identity provider. Switch on for higher security. | Toggle | Off | ||
SLO URL | The Single Logout endpoint URL of the SAML identity provider, which your IdP should display clearly within their own configuration page. This option tells Yellowfin where to point SLO responses. This is in the format of: <your_slo_domain>/<path_to_idp_slo_logout>For example, login.mybusiness.com/app/yellowfin1/ekti172b2ac0843Xf/slo | Required | None | ||
| Identity Provider SLO URL Response | This is an optional parameter which is only required if your IdP's endpoint for SLO responses is not the same as the one is uses for SLO requests. If nothing is entered, Yellowfin will use the URL entered in the Identity Provider SLO URL field. This is in the format of: <your_slo_domain>/<path_to_idp_slo_logout_response>For example, login.mybusiness.com/app/yellowfin1/ekti172b2ac0843Xf/sloreponse | Optional | None | ||
| Identity Provider Certificate | This certificate decrypts requests from the identity provider. Your identity provider should make this certificate obvious in their configuration. | Required | None | ||
Service Provider | Encryption Private Key | This private key decrypts incoming encrypted SAML requests from the identity provider. As mentioned earlier on this page, you must generate your own SSL key pair and provide the private key here. | Required | if the toggle for Incoming Requests Encrypted is enabledNone | |
Service Provider Certificate | This certificate verifies incoming encrypted SAML requests from the identity provider. As mentioned earlier on this page, you must generate your own SSL key pair and provide the encryption certificate here. | Required | None | ||
Signature Algorithm | This algorithm verifies the incoming identity provider certificate. Choose from three different hash lengths to match whatever your incoming certificate uses:
If you're not sure, use the default. | Required | RSA-SHA256 | ||
| Digest Algorithm | This algorithm verifies the incoming identity provider certificate. Choose from three different hash lengths to match whatever your incoming certificate uses:
If you're not sure, use the default. | Required | SHA256 | ||
Incoming Requests Encrypted | This toggle dictates whether incoming SAML requests will be encrypted by the identity provider. Switch on for higher security. | Toggle | Off if the toggle for Incoming Requests Encrypted is enabledNone | ||
UserId Attribute | This field holds the Yellowfin user ID (typically a username or an email field, depending on your system configuration). | Required | None | ||
Client Reference Id Attribute | This parameter provides the location of the Client Reference Id of the client org that the user belongs to. Normally, this is either left blank or set to ‘1’ for Yellowfin instances that have no related client orgs. | Not required | None | ||
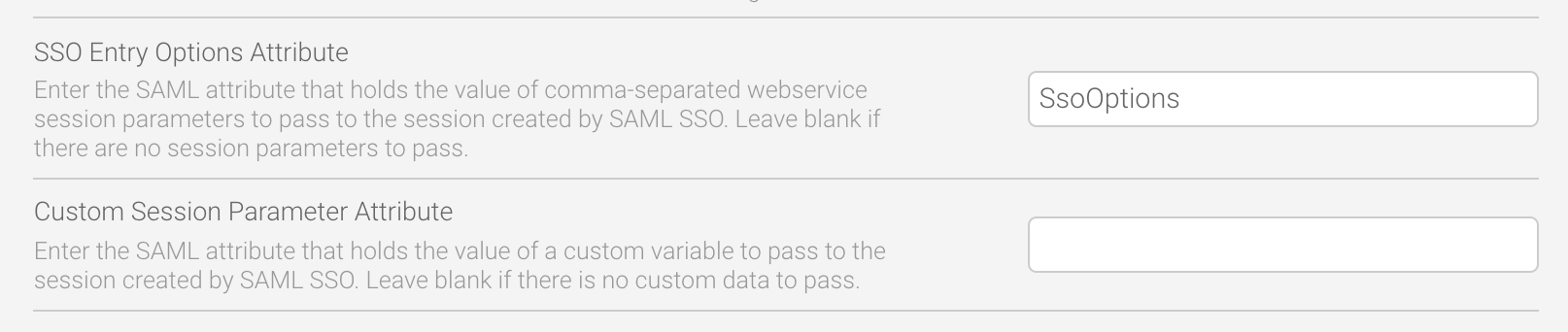
SSO Entry Options Attribute | This is a parameter takes the SAML attribute that holds comma-separated list of session parameters if you wish to automatically direct the user to a particular page or loginweb service session parameter values to be passed to the session created by the SAML SSO process. Leave blank to direct the user to their default entry page. See the Customize Data with CustomParameters and Parameters section for more details and an example. | Not required | None | ||
Custom Session Parameter Attribute | This field holds the value of a custom variable to passparameter allows options that can be passed via the Parameters option on an SSO web service call to be passed to the session created by the SAML SSO . Leave blank if there is no custom data to passprocess. This is attribute-based and can apply to individual users. | Not required | None | ||
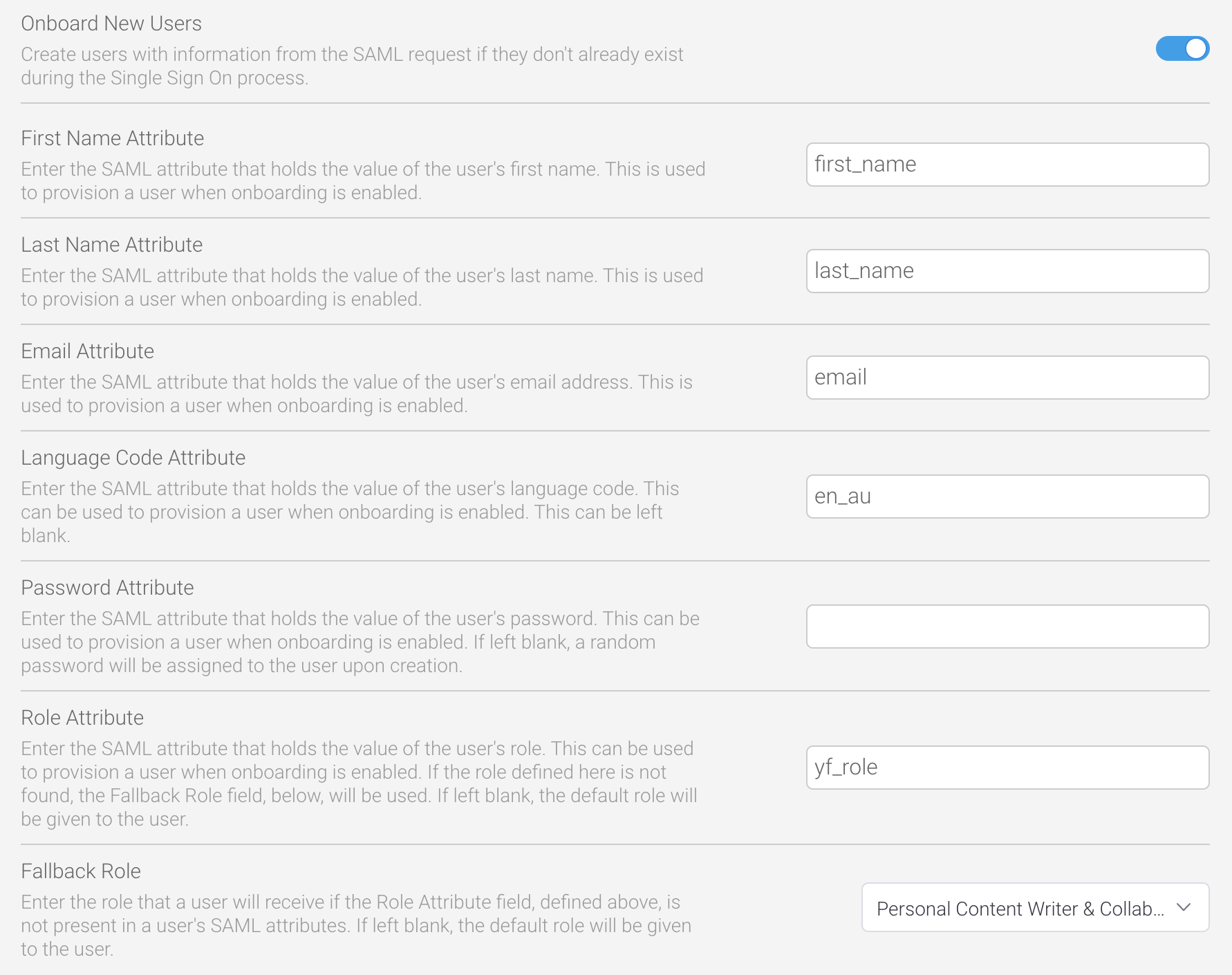
Onboard New Users | Enabling this toggle will allow SAML to provision new users automatically. If you don’t wish to provision new users, do not enable the toggle. | Not required | Off |
...
This page does not cover how to set up an identity provider, as there are many providers, each with different configuration processes. The page covers the basics that you will need to implement SAML for your Yellowfin users.
Setup SAML
| Styleclass | ||
|---|---|---|
| ||
...
Setup SAML
To configure a SAML provider, follow the steps below.
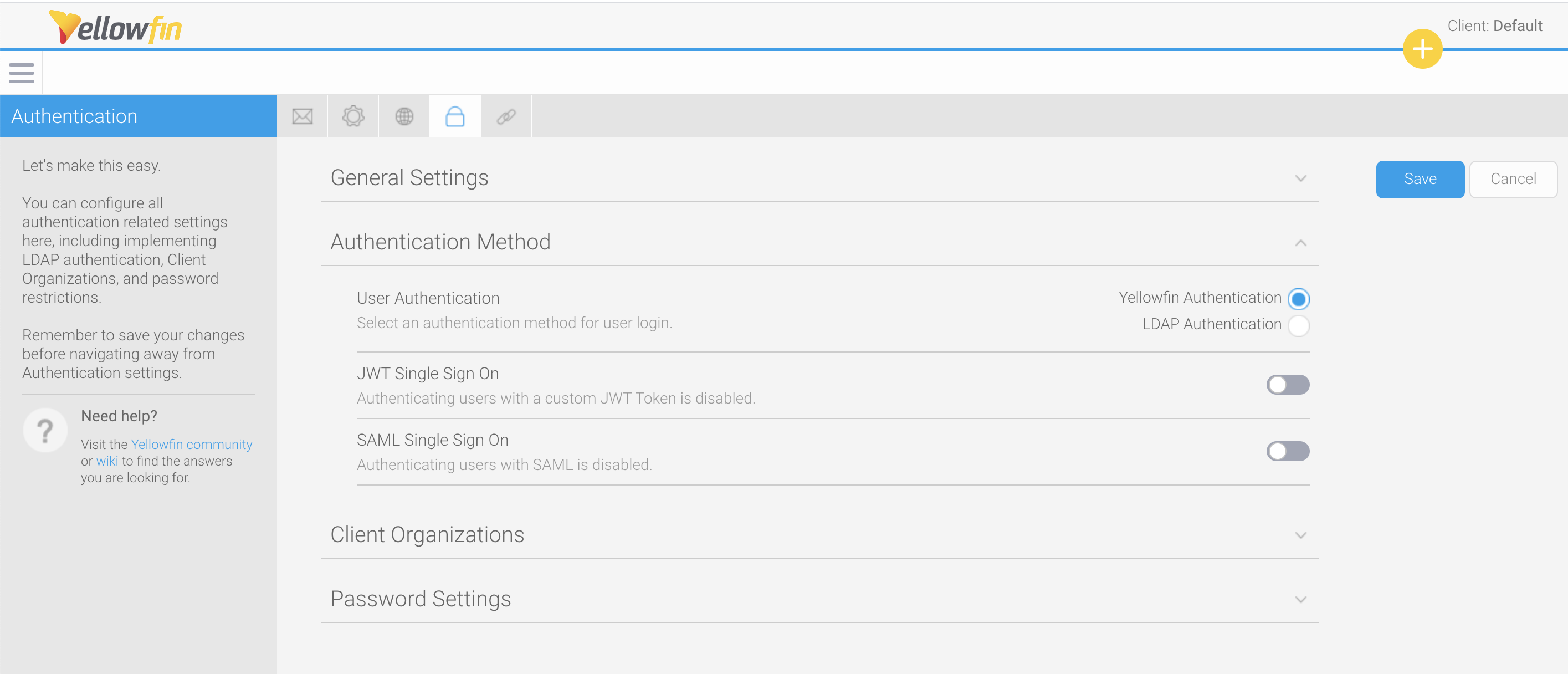
- From the Yellowfin burger bun menu in the top left corner, click on Administration, then Configuration
- Click on the Authentication tool (the lock), then on Authentication Method
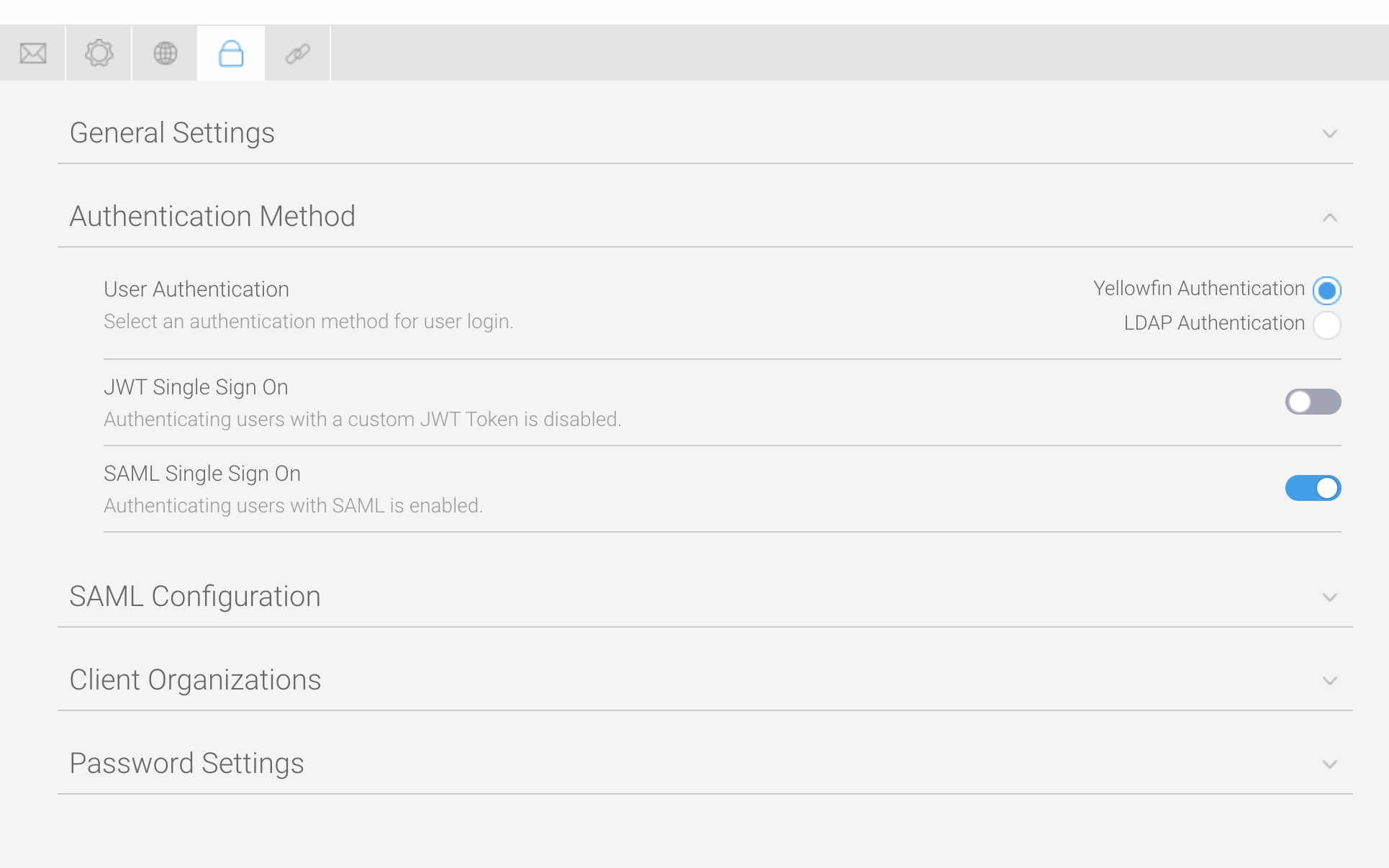
- Click on the toggle for SAML Single Sign On to enable it
A new section called SAML Configuration will appear. This is where everything related to SAML SSO is configured:
Click on SAML Configuration to expand the section - Refer to the preceding table to enter values for the required fields: Identity Provider EntityId, Identity Provider SSO URL and , Identity Provider SLO URL, Identity Provider Certificate, Signature Algorithm, Digest Algorithm, and User Id Attribute
- Refer to the preceding table and the following content to enter any other values for the other, non-mandatory fields described (see the image below for an example)
Enable SAML onboarding
| Styleclass | ||
|---|---|---|
| ||
...
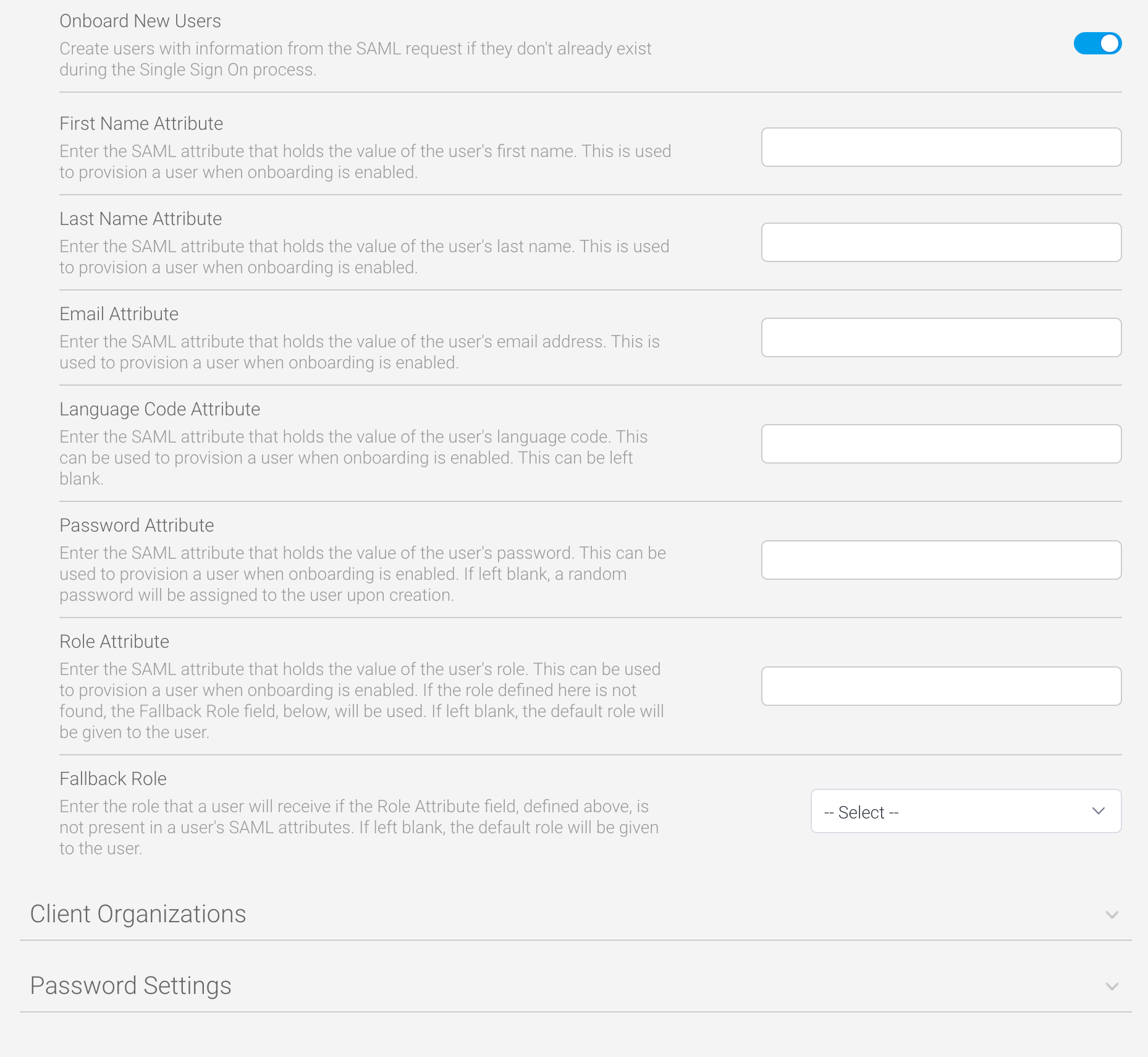
Enable SAML onboarding
Yellowfin can be configured to create new user accounts for any user who does not already exist in the system. This feature is called “onboarding”, and requires some additional configuration to provide Yellowfin with the information required to create new users from a SAML request. All of the following parameters must be set up and configured in the identity provider and Yellowfin to match the other attribute mapping parameters above.
...
- Ensure you’re in the same configuration screen described in the preceding steps
- Click on the Onboard New Users toggle to enable it
- Refer to the preceding table to enter values for the required fields: First Name Attribute, Last Name Attribute and Email Attribute
- Refer to the preceding table to enter any other values for the other, non-mandatory fields described (see the image below for an example)
Customize data with CustomParameters and Parameters
| Styleclass | ||
|---|---|---|
| ||
...
Customize data with CustomParameters and Parameters
If you already take advantage of the CustomParameters and Parameters options on an SSO web services call, these can also be added to SAML by using the fields SSO Entry Options and SSO Custom Session Variable Attribute.
SSO Entry Options
The SSO Entry Options field allows configuration of the available features in the resulting Yellowfin session after users log in via SAML. These are the same options that can be set on a web service SSO login using the ‘CustomParameters’ optionAttribute field allows custom data per user that can be passed via the CustomParameters option on an SSO web service to be passed to a session created by the SAML SSO process. This is attribute based, so it can be applied to individual users.
The SSO Entry Options Attribute field allows custom session variables to be set on a per-session basis when using SAML Single Sign On. The attribute can contain webservice SSO Session Options that will be applied to the session created by the SAML SSO process.. This is not attribute-based, so it applies to all users.
For example, if you want all your users a user to see their favourite reports, dashboards, stories etc. and so on when they login, you could use create a SAML attribute called SsoOptions with the TIMELINE and DISABLEHEADER and DISABLEHEADER parameters (or any others listed on theDefining Login Session Options wiki page). We’ll use these for our example below.
- In the SAML Configuration area of Yellowfin, locate the SSO Entry Options fieldAttribute field
- Type the name of your SAML attribute
Enter any parameters, separated by commas, that you wish to use
In our example below, we’ve used ENTRY=TIMELINE,DISABLEHEADER=TRUE - Click on the Save button to save your changes
You can test that your changes worked by logging in using your JWT SAML token and checking that the login options you’ve specified are displayed.
...
In Yellowfin, the only requirement is to add those details to the Custom Session Parameter Attribute field.
| horizontalrule |
|---|
| Styleclass | ||
|---|---|---|
| ||
...