Using LDAP means that Yellowfin access can be controlled externally, and organisation-wide, simply and quickly. Users can use their existing intranet password for Yellowfin, and reports can be given access restrictions which include or exclude users in specific LDAP groups. In addition, removal/lockout of the user in the LDAP directly will automatically flow through to Yellowfin, as Yellowfin has to authenticate via the directory for every login request, minimising the manual effort of mananaging users.
For Yellowfin to provision users automatically it has to assign a role to them. This role is defined as a Yellowfin 'Default' Role. In the Roles page, define one Role as the Default.
Note: if no role is set as default the users will not be provisioned correctly into Yellowfin and the process will fail.
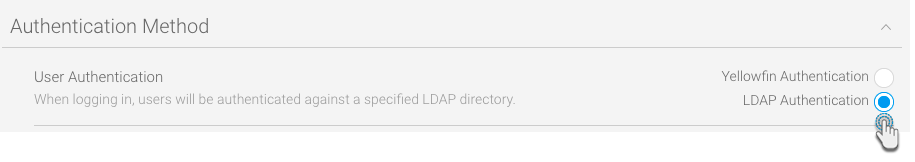
You will need to make sure that your instance of Yellowfin has the LDAP authentication functionality enabled.
Property | Description |
|---|---|
LDAP Host | LDAP server hostname or IP address. |
LDAP Port | TCP/IP port that the LDAP server is listening on. Set this to 389 for normal LDAP connections, or 636 for encrypted connections (that is, if no custom changes have been to the LDAP configuration). |
| Encryption | The encryption method implemented by the LDAP server. (Options include: None, TLS, SSL) This determines whether or not the LDAP connection would need to be encrypted. |
LDAP Base Distinguishing Name (DN) | The LDAP node that all users and groups are contained within. All your users might not be contained within a single group, so set the base domain here. Yellowfin will start searching for the LDAP directory from here. |
LDAP (Yellowfin User) Group | LDAP Group Name that identifies which users have access to Yellowfin. This group exists in the LDAP directory, not Yellowfin. Only members of this group will be able to log in to Yellowfin. |
LDAP Bind User | The username of the user with the rights to search the LDAP directory. The format of this username should either be in NETBIOS or full domain. For example: admin@Yellowfin.bi or YELLOWFIN\admin Note: It is not recommended to use an admin user. |
LDAP Bind Password | The LDAP password required for the Yellowfin application to connect to the LDAP directory; it authenticates the LDAP Bind User defined above. You must click 'Update Password" before testing your settings. |
LDAP Search Attribute | This is a unique User Name field that LDAP users will log in to Yellowfin with. You can find the LDAP attributes by opening the property box of an LDAP object and clicking on the 'Attribute Editor' tab. You can set most of these attributes to a value of your choice. The attribute name is what you will provide in the LDAP Search Attribute field. |
LDAP First Name Attribute | This maps to the First Name attribute of the user within the LDAP directory. This is so Yellowfin can match the user to a name and create an internal user account. |
LDAP Surname Attribute | This maps to the surname attribute of the user within the LDAP directory. This is so that Yellowfin can match the user to a name and create an internal user account. |
LDAP Email Attribute | This maps to the email address attribute of the user within the LDAP directory. This is so that Yellowfin can match the user to an email address for broadcast reports. |
LDAP Role Attribute | This maps to a Yellowfin Role to be assigned to the user instead of the Default Role. This way a user's role can be set in Yellowfin prior to their login. By default, users brought into Yellowfin via LDAP will have the 'Consumer & Collaborator' role. See RoleCode in OrgRole table. |
| LDAP Group Filtering Criteria | Criteria used to filter a list of LDAP groups. Only groups returned in the filtered list will be passed to Yellowfin. |
| Ordering | This order in which internal authentication is performed. Options include: LDAP Authentication First (default) or Internal Authentication First. This setting is important as it determines how Yellowfin will authenticate a user attempting to log in. |
Once defined, Yellowfin will automatically provision users as they attempt to login to Yellowfin for the first time.
Note: if the users in LDAP exceed the number of licences purchased, any new users will not be provisioned into the system.
| Setting | Parameter |
|---|---|
| LDAP Host | 192.168.4.241 |
| LDAP Port | 389 |
| LDAP Base DN | cn=Users,dc=i4,dc=local |
| LDAP Group | CN=Yellowfin Users,CN=Users, CD=i4,CD=local |
| LDAP Bind User | admin@Yellowfin.bi or YELLOWFIN\admin |
| LDAP Bind Password | ********* |
| LDAP Search Attribute | employeeID |
| LDAP First Name Attribute | givenName |
| LDAP Surname Attribute | lastName |
| LDAP Email Attribute | userPrincipleName |
| LDAP Role Attribute | Writer |
| Ordering | LDAP Authentication First |
Note: if a user is not found in the LDAP directory, it will look for the username as a standard Yellowfin user.